In the opening blog post of this series, we briefly introduced several common vulnerabilities that pirates exploit with ease to hack your video streaming service. In this blog and the next, we’ll take a deeper look into how pirates take advantage of OTT streaming security weaknesses.
Before diving in, however, let’s remind ourselves of what makes OTT video streams so tempting and susceptible to piracy. Unlike traditional pay TV services, which leverage anti-piracy hardware built into their set-top boxes, today’s over-the-top (OTT) technology has flipped the script… for good and for bad.
Why for good? Because it’s never been easier and more convenient for viewers to access your content.
Why for bad? The streaming devices used are open and unmanaged, so hackers can root and jailbreak legitimate devices, as well as reverse engineer applications to impersonate genuine apps, strip away your DRM protections, and bypass your protection mechanisms.
Let’s first look at today’s most common OTT service hacks.
Hack #1: Authentication tokens
DRM has been the standard technology for protecting content for decades. While DRM is used to encrypt content on one end and decrypt it at the other, a negotiation between service and client application to obtain the decryption keys always occurs. This negotiation is not part of the DRM standard, but it is implemented independently on each service platform. And it’s based on one of your greatest vulnerabilities – access tokens.
Take, for example, authentication tokens. When a user logs in and the client presents user credentials to the service, it authenticates the user and hands back an authentication token to the client. From that point on, the client doesn’t have to re-present the credentials. It only needs to present the token, upon which the service will immediately recognize that the user has been authenticated.
Think of the token as an airplane boarding pass. If all you had to do to board a plane is hand over a legitimate boarding pass at the terminal gate, then flying wouldn’t be secure. That’s why you also need to present a passport that includes your photo and matches the name on your boarding pass. But there’s one slight problem: authentication tokens aren’t compared against an ID. Anyone with a token “boarding pass” can board an OTT video service.
Authentication tokens may be hard to forge, but they’re very easy to abuse. Once the same user token is copied to another device, the service usually won’t be able to distinguish between the two.
Like many service providers, you’d probably prefer not having your customers type in their credentials repeatedly. That’s why authentication tokens are typically valid for long periods of time. Unfortunately, that makes them even more susceptible to abuse.
Hack #2: Authorization tokens
Once a user’s identity is established and the right to access certain content is verified, the client receives an authorization token for requesting access to the desired content. Pirates abuse authorization tokens like their authentication “cousin”, enabling multiple clients to gain access to content that was granted to another device or user.
Moreover, when a client uses an authorization token, it is often combined with a request generated by the device’s underlying native DRM system, typically Google’s Widevine, Apple’s FairPlay or Microsoft’s PlayReady. This joint request tells the service to grant a license to a particular DRM system based on the entitlement already granted and presented as an authorization token. Pirates, however, exploit this mechanism by using the authorization token from one device in combination with DRM systems of other devices.
Hack #3: Concurrency mechanisms
OTT services often employ a mechanism limiting the number of devices streaming concurrently on a single account. To enforce these limitations, each client sends a ‘heartbeat’ message to the service every few minutes while streaming. When the streaming stops, the client sends an ‘end session’ heartbeat message.
Pirates hack this mechanism in multiple ways. They send a fake end session to trick the service into thinking the session ended, even though streaming continues. Since the stream is provided by the CDN while the heartbeat is processed on the service operator’s backend, it’s not easy to correlate between the two.
In addition, pirates forge heartbeat messages so that they are sent from multiple devices despite appearing to be sent from a single device. And they can entirely suppress heartbeats to give the false impression of inactivity.
Hack #4: CDN tokens
Hackers have no problem exploiting unprotected CDNs: all they have to do is obtain the right URL to access their content.
However, even if you protect your CDN, pirates can easily get to your content. The streaming service typically grants a CDN access token, sometimes known as a “short token”. The CDN can then validate the short token and offer the client a CDN session token, aka “long token”, to be used throughout the viewing session, which usually lasts a few hours. While you can bind the token to an IP address, it’s quite rare as addresses may frequently change, causing the session to break.
Like other tokens, pirates can easily duplicate long tokens, enabling many clients to access the CDN freely. Attempts have been made to enforce one-time use of short tokens, but they are impractical and don’t address most of the vulnerabilities exploited by pirates, as we mentioned in a previous blog.
Hacks lead to costly service theft
By leveraging these hacks, pirates can often trick your service into giving them free access to content without having to break the DRM encryption. In some cases, pirates use a single account to stream content to tens of thousands of devices – all under the service’s radar. To make matters worse, such “service theft” leaves you with a huge streaming bill due to increased CDN costs.
What can you do?
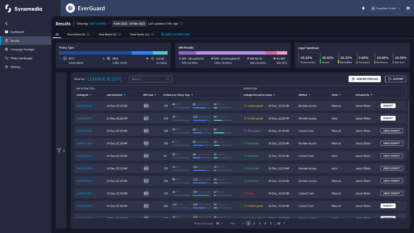
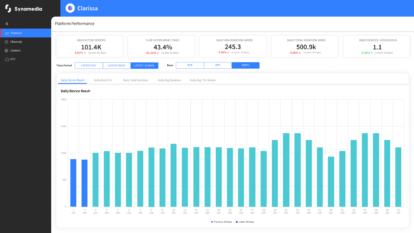
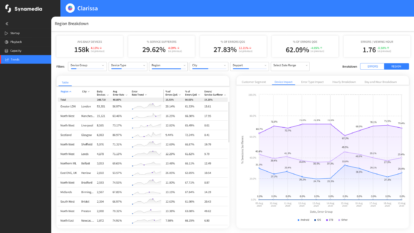
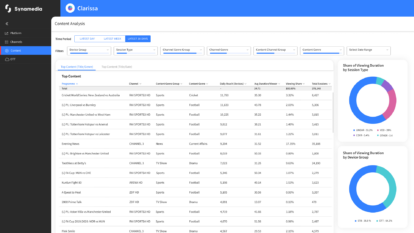
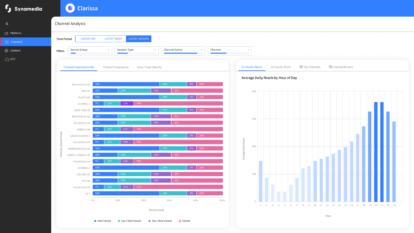
Fortunately, there are solutions that protect against the abuse of tokens. Synamedia OTT ServiceGuard, for example, robustly binds devices with an identity that cannot be cloned: each token or heartbeat is associated with that identity. When the token is used by the client, it sends proof to the service that the token was created specifically for that client. As such, the token cannot be transferred to another client and cannot be used to authorize another client. Token validation can also be carried out on the CDN to prevent short and long token reuse by multiple devices and to avoid servicing pirate scripts altogether.
Next up, mDRM vulnerabilities
After covering the most common OTT service hacks, the next blog in our series will show how pirates not only infiltrate and distribute legitimate services, but also steal content by exploiting multi-DRM (mDRM) systems. If you thought DRM is the gold standard for service protection, read our next blog to get the real picture.
If you’d like to discuss these issues further with our team of experts, get in touch.
About the Author
Nitsan Baider is a Director of Product Management at Synamedia. In his role he leads the development of new and innovative security solutions for streaming OTT service providers, taking them to market, and evangelizing them. Nitsan has spent many years in cyber security and has led several products in the past. He holds a B.Sc. In Mathematics and Computer Science from Tel-Aviv University. In his spare time, Nitsan enjoys playing piano.