If you’re a service provider streaming premium OTT video, chances are that as you read this blog, pirates are busy stealing — or at least trying to steal — content from your service to siphon your revenue. Even if you’ve managed to stay under the pirates’ radar until now, content owners are demanding that you comply with certain security requirements that require watermarking. Either way, piracy is impacting your industry… and watermarking for video is fast becoming an essential tool to securing your OTT business.
That’s why it’s not a question of if you need a video watermarking solution, but rather which type of implementation makes the most sense for you. In this blog, I’ll help you navigate the watermarking world so that you can make a more informed decision. I’ll cover the basics of video watermarking and also the main differences between the two main approaches: client and head-end watermarking. You’ll learn which approach is more effective in combating leaks to piracy from OTT services, and no less important, the reasons why.
Forensic watermarking: tracking the source of the leak
Before diving in, let’s briefly remind ourselves how video watermarking acts as a popular technology for tracking leaked video content through three basic steps.
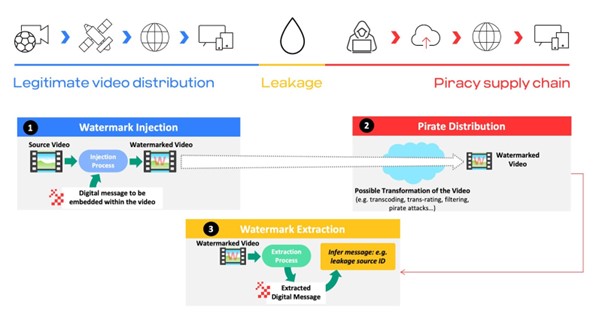
- Injection – You embed digital data (aka watermark), representing the subscriber or device’s ID, into the video stream.
- Pirate distribution – After the video is leaked, pirates swoop in to manipulate and distribute it to viewers.
- Extraction – You locate the leaked video on the pirate’s service, extract the watermark to determine the source of the leak, and take action that can include real time CDN session blocking for a specific account.
Client vs. head-end watermarking – What’s the best approach for OTT?
There are two prevailing forensic watermarking options available – client watermarking and head–end watermarking. Before pitting the two against each other, let’s briefly explain the approaches.
a. Client watermark
A client watermark is embedded into the video by the device – on the client side – usually by image overlay or blending. The image may be generated either by the client or at the head–end, after which it is delivered to the client. Since a device has limited computational resources for generating an image or cannot access the video content for security reasons, OTT client watermarks are content unaware. This means that the watermark is embedded within the frame without taking into account the displayed video content. Even though a forensic content-unaware watermark is considered to be covert, “golden eye” experts can still notice it when embedded in certain content. In addition, in order to overcome piracy attacks, blending visibility and intensity of the client watermark must increase, making it more discernible to others.
b. Head-end watermark
A head–end watermark is embedded in the video stream before it reaches the client device. It is typically implemented via A/B sequencing or variant watermarking, and may even be carried out by CDN edge embedding. In A/B sequencing, two versions of the same video – A and B – are created with non-visible differences in each segment. Each client receives a different adaptive bit rate (ABR) segment sequence, with the contiguous sequence representing a unique ID for the service user. Crucially, when compared to client-side watermarking, Head-end watermarking does not require any modification of OTT client software.
Why client watermark?
Now let’s determine which of the two approaches is best for your OTT service. First, we’ll have a look at how a client watermark stacks up against some key factors you need to consider when choosing a solution.
- Robustness
When it comes to robustness against pirate attacks, client watermarking offers mixed results. On the one hand, since the entire ID is usually in a single frame, the watermark is more resistant to temporal collusion attacks. On the other hand, since a client watermark is typically content unaware, as mentioned above, its ability to overcome severe distortion and spatial collusion attacks is likely to be compromised by visible artefacts that impact your viewers’ user experience. More importantly, given that the client watermark is embedded in the client of an unmanaged device, it is highly vulnerable to various watermark avoidance methods. Client watermark is especially vulnerable to CDN leeching, where pirates exploit DRM vulnerabilities and token duplication to steal content from the CDN using non-legitimate device and applications. In addition, its security is tightly bound to the DRM, since, as soon as the DRM is breached, and recent history has shown it happens, pirates will be able to decrypt content without going through the client watermarking agent.
- User experience
We just established that the more robust a client watermark is to piracy attacks, the more visible it will be, because a client watermark on an OTT device is usually content unaware. For example, to resist camcorder-based strong distortion or to overcome advanced spatial collusion attacks, the watermark’s visibility increases. Beyond the trade-off between robustness and minimal visibility, you also need to take into account the trade-off with video extraction duration. That is to say, in order to ensure that your watermark remains robust and relatively indiscernible, you need more time to extract it from the content.
- Deployment and maintenance
Regarding deployment and maintenance, a client watermark again has its trade-offs. You may think that in order to deploy a client watermark, all you require is a simple SDK. However, a basic SDK covers only a few devices, while in all likelihood you’re supporting myriad, ever-changing device flavours. If we know anything about pirates, once they realize you’ve tracked them down, they will find your weakest link – in this case, client devices not hardened against watermark avoidance. The problem is that hardening all of your unmanaged client devices is an extremely expensive, complex and slow proposition. That’s because hardening greatly depends on the specifics of each client platform technology, which keep changing among today’s OTT clients.
Why head-end watermark?
- Content awareness
Since, by definition, the head-end watermark is located in the head-end rather than in the device, it can leverage significant computational resources. In most cases, the head-end watermark is content aware, making it studio-compliant and meeting the golden-eye standard of an imperceptible, artefact-free watermark. Moreover, as a content-aware watermark, it can optimize robustness (to distortion and spatial collusion), visibility, and video extraction duration. A client watermark, in contrast, can meet only two of the three criteria in a given setting.
- Robustness
Another advantage of the watermark residing in the head-end is that, by design, it is far more resistant to watermark avoidance. And while a head-end watermark may be subject to temporal collusion, there are algorithmic solutions available to address such an attack without impacting visibility.
- Deployment and maintenance
When it comes to deployment and maintenance, the head-end watermark stands head and shoulders above the client watermark. Deploying head-end watermarking requires a one-time integration covering myriad current and new OTT devices, no DRM integration, and no device hardening. In contrast, since a client watermark covers a limited number of devices, it requires ongoing, time-consuming integration with newly introduced devices. In addition, a client watermark is dependent on DRM integration for hardening, and needs to continually undergo software upgrades as the devices used by your viewers evolve.
Not all trade-offs are equal
As we’ve seen, both the client watermark and head-end watermark encounter trade-offs. However, the impact of these trade-offs on each of the approaches differs significantly.
Take, for example, protecting key content properties such as live sports. If you use a client watermark, then you can extract it within a couple of minutes. However, if you focus on minimizing extraction time, you may end up failing to detect any content leakage whatsoever. That’s because the client watermark can be removed from non-hardened devices, making the shorter video duration time for extraction irrelevant. So, you might ask: Why not harden all of your client devices to give you 100% coverage against watermark avoidance? No go: your deployment and maintenance costs would be way too prohibitive.
In contrast, even though a head-end watermark requires a slightly longer video recording for extraction, it will detect your content leakages in most circumstances. By design, the watermark always addresses avoidance attacks and never requires client device hardening, regardless of the quantity and frequency at which new devices are added across your service.
And the winner is…
So, if you are an OTT provider delivering premium content to viewers across myriad devices, then it’s obvious which video watermarking approach is recommended. As we’ve shown, the head-end takes the client/device out of the equation to reduce risk and ongoing integration complexity. It also avoids a trade-off between visibility and robustness, even though the watermark requires a slightly longer time for extraction compared to a client watermark. Most importantly, it is not vulnerable to any watermark avoidance method, regardless of client manipulation. Given these advantages, it’s no wonder that head-end watermarking is increasingly becoming the approach of choice for OTT service providers worldwide.
Get in touch to learn more
Now that you’re aware of the merits of a head-end watermarking solution, get in touch to discuss how Synamedia ContentArmor can help your streaming service detect and prevent video piracy.
About the Author
Alain Durand is Senior Director of Synamedia ContentArmor. Prior to joining Synamedia, Alain worked as a security expert in the digital television industry for more than 20 years. From 2008 to 2013, Alain served DVB as chairman for Content Protection Technical Module, which is issued several sets of specifications, which are now re-used for instance in broadcast security systems such as BISS-CA. In 2016, he created ContentArmor, a leading vendor of forensic watermarking, bought later in 2021 by Synamedia.