For premium video services, piracy is no longer a theoretical risk. For live sports, early-window movies, and high-value series, illegal re-streams can appear within minutes — sometimes seconds — of first availability.
Digital rights management (DRM) controls access, but once a stream escapes the ecosystem, a different question becomes critical:
Whose copy is this — and how quickly can we act?
That’s where invisible forensic watermarking earns its place in modern content protection strategies.
Invisible watermarking: attribution, not access control
Invisible (or forensic) watermarking embeds an imperceptible identifier directly into the video signal. Unlike DRM, which enforces playback rules, watermarking enables attribution: when a pirated copy is discovered, the watermark reveals which legitimate session, account, or distribution point it originated from.
In adaptive streaming environments, watermarking is most commonly implemented using A/B watermarking:
- Each video segment exists in two slightly different variants (A and B).
- A unique per-viewer sequence is created by choosing A or B over time.
- That sequence encodes the viewer or session identity.
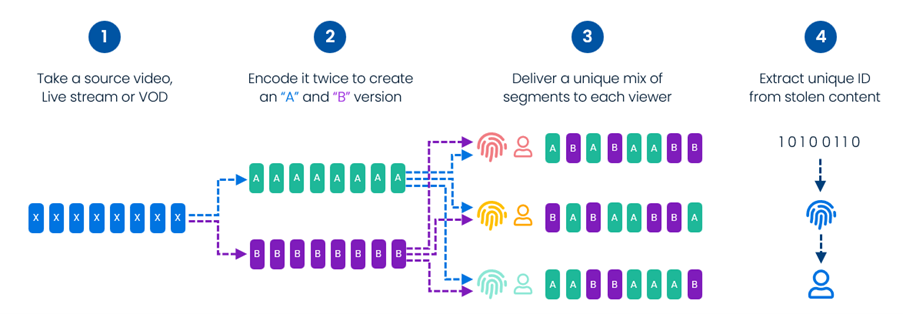
This approach is well understood, widely deployed, and standardised within the DASH ecosystem. It integrates cleanly with existing ABR workflows and scales well across CDNs.
But it also comes with some very real constraints.
The practical limits of traditional A/B watermarking
A/B watermarking encodes identity one bit per segment. In practice, that means:
- Detection confidence builds gradually over multiple segments.
- Longer segments or disrupted playback increase time-to-attribution.
- Identification depends on receiving a sufficiently long, continuous sequence.
Pirates know this.
Rather than trying to “remove” a watermark — which is extremely difficult — sophisticated attackers focus on disrupting detection:
- switching between multiple sources,
- introducing gaps or jitter,
- splicing streams together,
- deliberately breaking sequence continuity.
The watermark is still there — but attribution takes longer. And in piracy operations, time is money.
Every extra minute before identification is another minute of monetisation.
Why speed now matters more than perfection
The goal of modern watermarking isn’t theoretical robustness. It’s operational effectiveness:
- How quickly can a leaked stream be identified?
- How fast can the offending session be disrupted?
- How much pirate dwell time can be eliminated?
Reducing the time window to actionable confidence has become the defining metric.
This is where edge watermarking fundamentally changes the equation.
Edge watermarking: removing the one-bit-per-chunk constraint
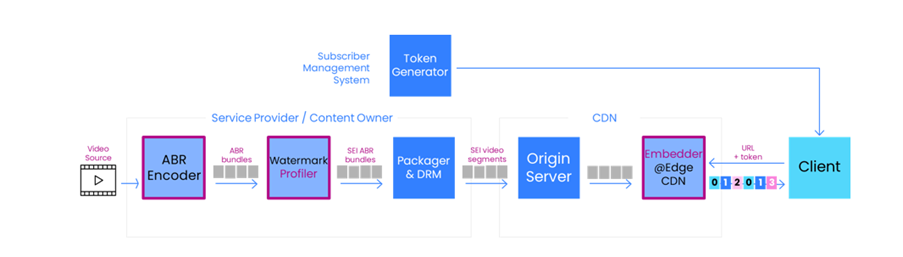
Edge watermarking shifts watermark insertion from the head end to the very edge of the CDN, leveraging edge compute and compressed-domain watermarking techniques uniquely enabled by Synamedia ContentArmor.
Rather than pre-generating and switching between A/B variants, watermark payloads are inserted dynamically at the edge, directly into the compressed video – even on encrypted content – without full decode and re-encode.
This architectural shift delivers several important advantages:
1. Faster payload accumulation
Watermark insertion is no longer tied to segment boundaries or limited to one bit per chunk. Payloads can be embedded at a higher effective rate, allowing identification confidence to build earlier in the stream.
2. Reduced effectiveness of sequence-breaking attacks
Because watermarking is self-synchronising and independent of rigid segment sequencing, common pirate tactics — dropped segments, jitter, and stream splicing — are far less effective at delaying attribution.
3. Lighter head-end, simpler workflows
The head-end no longer needs to manage variant explosions or tightly synchronised insertion logic. Complexity moves to where scale already exists: the CDN edge.
4. Security preserved end-to-end
Watermark insertion occurs without exposing clear video, maintaining existing encryption and DRM trust models while adding forensic traceability.
In internal proof-of-concept testing, this approach demonstrated tens of milliseconds of additional edge latency at high percentiles — a small and predictable trade-off for materially faster detection and disruption.
Turning the pirates’ advantage into a disadvantage
Pirates exploit the natural latency of watermark detection. ContentArmor Edge watermarking flips that dynamic.
By shortening the time needed to reach attribution confidence, edge watermarking reduces:
- pirate monetization windows,
- operational response delays,
- and revenue leakage during live and early-release events.
It doesn’t claim to make piracy impossible — nothing does. It makes piracy less profitable, less persistent, and easier to disrupt.
That’s the real win.
What’s next
At Synamedia we’ve fused our industry-trusted ContentArmor technology with our video-centric CDN product Fluid Edge, representing a meaningful evolution in content protection: one that aligns watermarking speed with the realities of modern piracy and live streaming economics.
We demonstrated ContentArmor Edge Watermarking—including encrypted, compressed-domain watermark insertion at the CDN edge—at NAB 2026.
If you’re rethinking how quickly your organisation can move from pirate detection to decisive action, we’d welcome the conversation.