OTT service theft: Why DRM isn’t enough to protect your streaming service
In the second post of our series, we described how pirates exploit various tokens to carry out common hacks on video streaming services. In this post, we’ll look at the vulnerabilities of DRM from two different perspectives. Firstly, how pirates exploit DRM vulnerabilities to gain access to and re-distribute your OTT streaming services. Secondly, how they breach your CDMs to steal your content. And, regardless of which path(s) pirates choose, why DRM falls short and fails to stop them in their tracks.
DRM has a long, rich history in protecting video content. Over time, three main DRM systems – Google Widevine, Apple FairPlay and Microsoft PlayReady – dominated the market. To enable efficient multi-DRM (mDRM) use, they also agreed on a set of standards allowing streaming services to encrypt their content once and use each DRM system to securely distribute keys to each type of device. As a result, in order to operate these DRM systems, you need an mDRM system that protects your content with a single key rather than three separate keys.
Enabling service theft: Unauthorised access strikes again
Pirates exploit DRMs in one of two ways: service theft and content theft. Let’s start with service theft.
As discussed in our previous blog post, when a client uses an authorisation token, it is typically combined with a DRM license request generated by the device. By nature, the DRM system is concerned only with key distribution and encryption/decryption, but not with authorisation. The request tells the service to grant a licence to a particular DRM system based on the entitlement already granted and presented as an authorisation token. Pirates, however, exploit this by using the authorisation token together with different DRM systems. This enables hackers to easily obtain all required keys to the service, access the service, and distribute it to thousands of other pirates.
Enabling content theft: Breaching your CDMs
The most secure part of the DRM client is the content decryption module (CDM); that’s where keys are safely extracted and used to decrypt content. CDMs using special hardware called L1 CDMs provide the highest level of content security. Those leveraging software are referred to as L3 CDMs, and they are more prone to breaches.
The good news? It’s possible to identify a breach and provide a patch. The bad news? It can take months for it to happen. And since there are more than enough breached L3 CDMs out there, after one gets fixed, there’s always another one ready to be exploited.
While far less common, L1 CDM breaches exist, and revoking them is no small feat – a fix can end up permanently cutting off content access to an entire set of devices. To make matters worse, a hacked L1 CDM can enable pirates to access your high-quality content such as 4K files and streams.
Adding fuel to the fire
Many service operators are either unaware of, or ignore, the fact that they don’t optimise their use of DRM. Here are three examples of DRM misuse accompanied by a recommended best practice. With that said, implementing these recommendations won’t stop pirates from taking advantage of DRM vulnerabilities. But at least they’ll force pirates to work harder to steal your content.
Issue #1: Rotating keys infrequently
Even though DRM supports key rotation, most deployments prefer to keep things simple by using the same key for extended periods. When pirates don’t have to change their keys frequently, if at all, they can set up scalable, uninterrupted operations far more easily. The lack of key rotation also helps pirates write easy-to-use scripts, enabling them to access encrypted content and then decrypt it.
Our recommendation: Rotate keys frequently.
Issue #2: Using the same keys for all content types
Video streams include various content types such as video, audio and subtitle tracks. In addition, video is available at different resolutions and bitrates to serve different quality levels. Typically, streaming services use the same keys regardless of content type. Therefore, for pirates to get their hands on high-quality content, all they need to do is access easily obtainable content — for example, an encrypted audio track — and extract keys from it.
Our recommendation: Use different keys for audio and video, as well as for high-quality (4K) and lower resolution video.
Issue #3: Allowing high-quality content on any device
Given that mobile and open devices are ubiquitous in today’s OTT streaming video era, service providers often allow high-quality content, which is in great demand, to appear on low-security-grade devices such as browsers. It’s no surprise that pirates jump on this vulnerability to increase their competitiveness against your legitimate service.
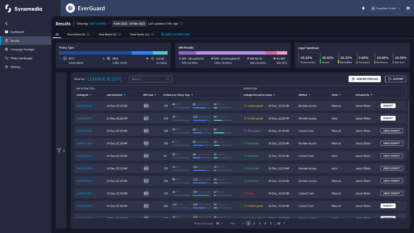
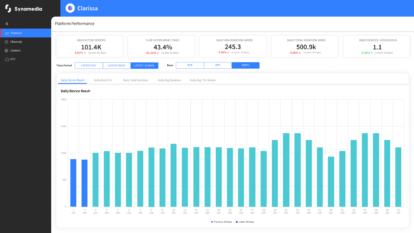
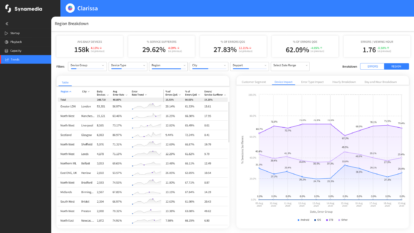
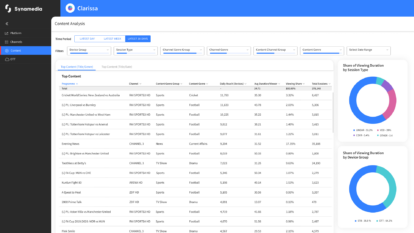
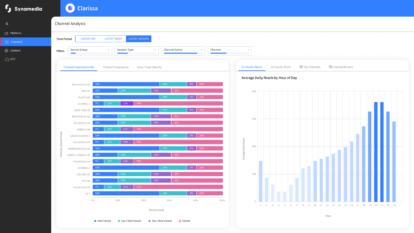
Our recommendation: Consider limiting the availability of your premium, high-quality content – such as 4K streams – to devices with L1 CDMs. To guard against L1 breaches consider additional protection. For less secure L3 devices receiving high-quality streams consider additional protection such as that provided by Synamedia OTT ServiceGuard.
Introducing the gamechanger: Piracy scripts
As we’ve seen throughout this blog series, ever since OTT arrived on the scene, pirates have become masters at exploiting video streaming services and stealing content. So, why are pirates a much bigger threat today than in the past?
The short answer: scripts.
In our next blog, we’ll show you how these readily available programs make piracy easy, scalable and a huge threat to your business. And naturally, we’ll reveal the one step you can take to stop piracy and prevent pirates from accessing your service and stealing your content.
Get in touch if you’d like to discuss further any of the topics raised in this series.
About the Author
Nitsan Baider is a Director of Product Management at Synamedia. In his role he leads the development of new and innovative security solutions for streaming OTT service providers, taking them to market, and evangelizing them. Nitsan has spent many years in cyber security and has led several products in the past. He holds a B.Sc. In Mathematics and Computer Science from Tel-Aviv University. In his spare time, Nitsan enjoys playing piano.